When we talk about encrypted communication, we have to keep in mind two parties primarily; the sender and the receiver. The former encrypts and the latter decrypts. Described as the foundation of Public Key Infrastructure (PKI), Asymmetric Encryption key provides ...
Snabay Networking Latest Articles
What is a Honeypots in Network Security

If you look up the history of cyber crimes(honeypots), there you can find a lot of creative and unique ways that attackers use to victimize their targets. With the possibility of different types of attacks targeting different functions and trying ...
Enterprise Non Public Network (Private Network)
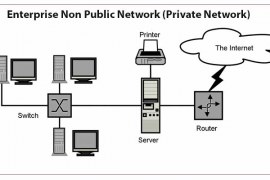
Enterprise Non-Public Network (Private Network): In this age of the internet, all users connected to the internet can send and receive data publicly. But in its primitive form, computer networks were formed by organizations such as universities, military, and research ...
Campus Area Network (CAN) With Example

Campus Area Network was shortly called the CAN. Office, school, any area that presented at a limited distance is called the campus. The Providing of the network at a particular location is called a Campus Area Network. Now How the ...
History of Local Area Network (LAN)
As the world started to get more technologically advanced after the two devastating world wars which changed the power dynamics of the entire world, use of computers in United States of America, one of the few involved parties in the ...

