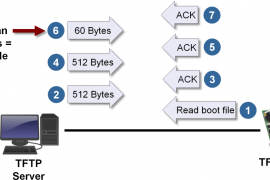
TFTP (Trivial File Transfer Protocol) is a file transfer protocol like FTP that is used to transfer the files. It uses the UDP (user datagram protocol) In order to transfer the files from one end to another end. This protocol ...
Snabay Networking Latest Articles
What is EtherChannel PAgP and LACP Modes

Port Aggregation protocol: PAgP was marketed under or related to cisco systems It helps more than anything else in creating automation of EtherChannel links, port aggregation protocol packets exchange between EthernetChannel ports, in order to form or establish the connection ...
What is Circuit Switching and Packet Switching

Circuit Switching Circuit switching is a technique of connecting the network of telecommunications where two meeting points of the network make a dedicated channel of communication (circuit) through the system of that network before the communication of these nodes. The ...
What is Certificate Authority, Digital Certificate
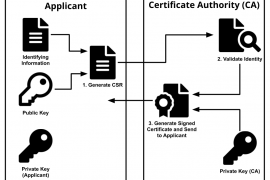
Certificate Authority in the Digital world refers to the entity that issues Digital certificates for the key holders in Cryptography Encryption. This certificate is given to the public key holders, who becomes a part of the Public Key Infrastructure (PKI), ...
Types of Honeypots – Low Interaction Honeypot and High Interaction Honeypot
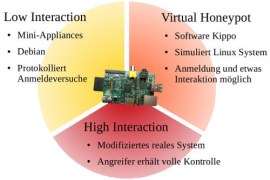
In the wake of the advanced and almost impossible to prevent cyber attacks that have victimized literally millions of people and posed serious cybersecurity questions that needed to be answered, some of the measures taken have finally given some relief ...
Difference Between Firewall and Intrusion Detection System
As useful as it may be, the internet is a dangerous place. It came into the existence in 1983 and since then it has been growing and advancing at a surprisingly high speed. Its’ growth and development have made our ...
Types of Computer Networks on the Basis of Area

Types of Computer Networks on the Basis of Area: Computers used to be standalone devices once. They were bought and required a lot of manpower to operate. They were limited in application. Once the computers got smaller, smarter and faster, ...
What is Domain Controller in Networking
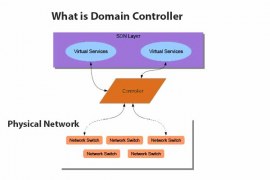
We all know how to use a computer or a laptop and the first thing we do before we can use either of them is log in by using the security password. But what happens when you are an employee ...
Ring Topology Advantages and Disadvantages
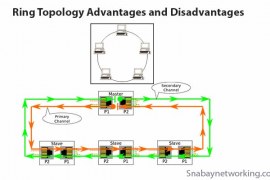
Ring Topology is basically a circle of connected devices where one node is connected to two nodes, one on the left and one on the right, making a ring consisting of at least 4 computers. One device sends the data ...
Types of Network topology
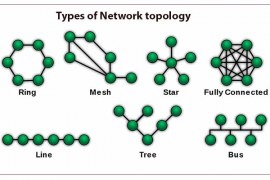
Computer Network Topology or simply Network Topologies is a virtual structure consisting of links and nodes which sometimes is called the network architecture. The job of the Network Topology is to define how two devices are connected to each other ...