Phishing Attack
Phishing and Pharming Spoof Attacks: The phishing attack is a cyber-attack in which a user is redirected to an illegitimate and unauthorized website which is disguised as a legitimate one. The purpose of this attack is to extract sensitive and personal information from the users. Now this attack may seem similar to a DNS Spoofing attack but it is not. To know more about the Phishing and Pharming Spoof Attacks keep reading this article till the end you will get to know more about this.
In a DNS Spoofing attack, the DNS server is directly corrupted while a Phishing attack comes in an email or text message with an attached link to the fake website. The important thing to remember here is that these illegitimate and unauthorized websites appear as legitimate because they are designed to resemble them. It is a part of the deception and to gain the trust of the users because anyone rarely provides their login credentials and credit cards detail to the websites they don’t trust.
When this malicious email comes we have no way of knowing the intention of the sender since most email servers is not programmed to verify if the sender has the authority to send this type of email. Thus the defense is weekend on this point.
Phishing attacks are carried out by a botnet created using a remote device. The number of spam emails, which these malicious emails are called, decreased as much as 50 percent in the USA in 2017 but they are still the most trusted carrier for spreading malware across networks. The most common type of phishing is Deceptive Phishing.
Also read…
- Types of Network Attack – Man in the Middle Attack (Cyber Attack)
- Types of Network Attack – DNS (Domain Name System) Spoofing Attack
Pharming Attack
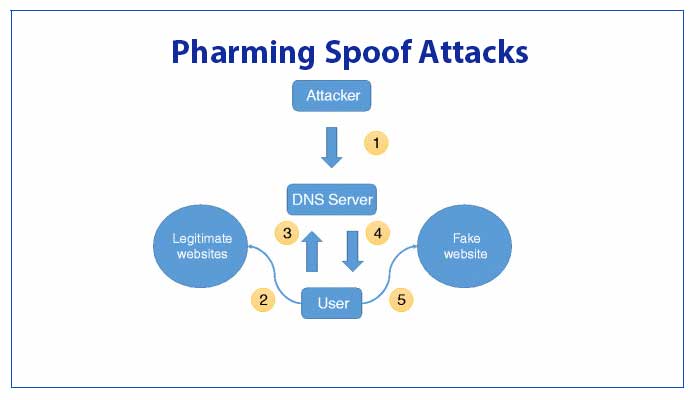
To redirect a user to an illegitimate website, either the DNS server is poisoned or host files on the computer are changed in the pharming attack technique. Unlike phishing, pharming relies on the unprotected computers to launch the attack instead of targeting a server, therefore, Pharming attacks are mostly directed at individual users for which they are better suited since Desktop are more vulnerable and unprotected. Even though phishing and pharming hold similarities and differences, they both are used for online identity theft and financial theft.
Even though the main target of the pharming attack is the host files, it may cause more harm in the network router by compromising it as a whole, even the Local Area Network (LAN) is threatened. After the attack, the compromised router passes the corrupted Domain Name System (DNS) data. Sometimes, in a process called Drive-by Pharming, the DNS server is completely replaced by malicious JavaScript. In some cases, Firmware is replaced instead of the DNS server.
Download Phishing and Pharming Spoof Attacks in pdf – Click here