A Network Switch is a networking device helpful to connect multiple devices. Like if we have 10 computers then we can connect computers to the ports of the Network switch for the local communication and it works on the second last layer of the OSI model i.e. Data link layer. It uses mac addresses to make decisions. It has per port collision domain and single broadcast domain like if we have 48 ports switch then there are 48 collision domains and 1 broadcast domain.
A collision domain is a part of the network wherein packets may collide. When one or more devices send packets across the shared channel at once then it may lead to a collision and thus reduces the efficiency of the network. After the collision, packets need to be sent again by the device but a single device at a time to complete the transmission of the packets. A domain broadcast is the boundary of the network up to which your packets may travel. All the ports of the Network switch come under a single domain of broadcast i.e. if you send packets the first time then the packets will be broadcasted to every machine connected to the switch.
A domain broadcast is the boundary of the network up to which your packets may travel. All the ports of the Network switch come under a single domain of broadcast i.e. if you send packets the first time then the packets will be broadcasted to every machine connected to the switch.
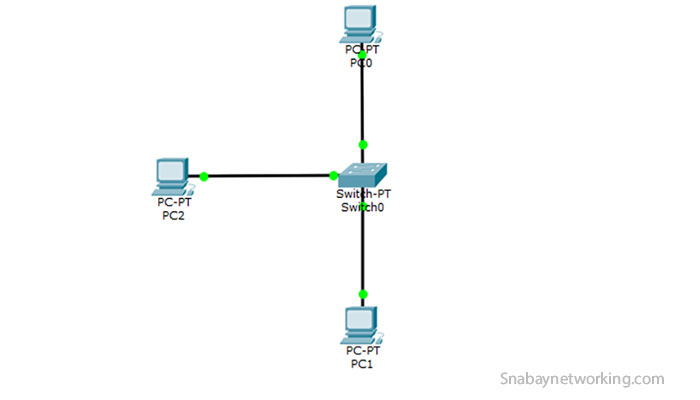
In the above picture we have 7 collision domains and 1 broadcast domain.
Moreover, switch works on the network Star topology wherein each node or device is connected to the centralized device i.e. a Switch.
How a Network Switch Works
In every network card, there is mac address burned out and it is of 48 bits or 6 bytes. This mac address is used among the devices for communication. If two machines want to communicate then both the machines should know the 6-byte mac address of each other before sending out the packets.
As we know switch decides what needs to be done after seeing the mac table or CAM table which is nothing but the entries of mac address received on the switch ports. This mac address table is saved in the ram of a switch, once the switch is restarted and there is power failure then all the mac entries are gone. Following are the processes performed by the switch:
- Learning: The switch only learns the mac address when it receives the frame i.e.the source mac address.
 If I want to ping PC2 from PC0 then Switch updates the mac table and thus mac address of PC0 is stored along with the port fa0/4 on which it is received. The same goes for PC2, mac address of PC2 is stored along with the port fa0/3 on which it is received.
If I want to ping PC2 from PC0 then Switch updates the mac table and thus mac address of PC0 is stored along with the port fa0/4 on which it is received. The same goes for PC2, mac address of PC2 is stored along with the port fa0/3 on which it is received.
- Forwarding: Switch does two types of forwarding after seeing the mac or CAM table:
- Unicast: The Switch only does this type of forwarding when it has the host mac address entry in the CAM or mac address table.
- Unknown Unicast or Broadcast: The Switch does this type of forwarding when it receives unicast frame or destination mac address and it does have the entry for the host mac address in the mac address or CAM table then it will broadcast the frame to all the ports of switch except the port from which unicast frame received.
- Filtering: When a unicast frame is received on the switch port, then switch checks the host mac address and see in the mac address or CAM table whether the entry is available for the host mac address or not if entry is available then it will be forwarded only through the particular exit interface and thus it won’t be broadcasted.
- Loop Avoidance: If we are using multiple switches and to provide redundancy we are using several links or connection between the switches then it may create layer 2 loops and as a result, we may face CAM table instability, Broadcast storm. The switch uses STP( Spanning tree protocol) to avoid switching loops. It puts the one connection or link in the blocking state. When the main link gets down then the blocking state link comes into the picture and starts to forward the frames.
Moreover, the Maximum-Aging timer for the host entries in the mac-address-table or CAM table is 5 minutes or 300 seconds. However, we may change this max-age timer by using the commands.
You may see the CAM table by using the command show mac-address-table. As you can see in the above picture mac address or CAM table has four entries:
As you can see in the above picture mac address or CAM table has four entries:
- Vlan: It indicates the VLAN number configure for the switch port. Like in the above pic VLAN number 1 is configured for all the ports of the switch and it is by default. However, we may change it.
- Mac Address: It shows the mac address of the device which is attached to the particular port of the switch.
- Type: It indicates how the switch has learned mac address of the device mac address. There are two types: Dynamic and static. We may manually set mac address of the device and for that case, the type will be static.
- Ports: These are the port numbers of the switch and you will find the mac address entries attached to these ports.
Let’s understand how a switch works:
Let’s say I want to ping PC5 from PC1, as we can see there is no entry available in the mac address or CAM table of the switch.
 When I ping PC5 from PC1 then first it generates the ARP request to know about the mac address by using the Ip address of PC5 and this arp request will be forwarded to all the ports of the switch except the port from which it is originated then in return, the only PC5 gives the ARP response to PC1 and afterward, ICMP packet will be forwarded. As we can see in the picture firstly PC1 generates ARP request and after knowing the mac address of each other, the actual ICMP packets transmission started.
When I ping PC5 from PC1 then first it generates the ARP request to know about the mac address by using the Ip address of PC5 and this arp request will be forwarded to all the ports of the switch except the port from which it is originated then in return, the only PC5 gives the ARP response to PC1 and afterward, ICMP packet will be forwarded. As we can see in the picture firstly PC1 generates ARP request and after knowing the mac address of each other, the actual ICMP packets transmission started.
After the whole process,  the switch has the entries in the mac address or CAM table. On switch port f0/2 there is a mac address entry of PC5 and on switch port f0/4 there is a mac address entry of PC1.
the switch has the entries in the mac address or CAM table. On switch port f0/2 there is a mac address entry of PC5 and on switch port f0/4 there is a mac address entry of PC1. Moreover, these entries will remain in the mac address or CAM table for the 5 minutes. After 5 minutes all the mac entries will be gone and then again the arp request needs to be generated to find the destination address.
Moreover, these entries will remain in the mac address or CAM table for the 5 minutes. After 5 minutes all the mac entries will be gone and then again the arp request needs to be generated to find the destination address.
Difference Between Hub and Switch
A Hub is also a network device that is not used in today’s world. It works on the physical layer of the OSI model and similar to switch that is you may connect several machines to a particular LAN Network but the working of the hub is different from switches. It has one collision domain and a single broadcast domain that means only one device may forward packets at a time over the shared network medium. 
A Hub runs on Half-duplex and thus uses CSMA/CD( Carrier Sense Multiple Access with Collision Detection) to avoid collisions on the shared network segment. This CSMA/CD mechanism helps devices to know when is the right time to send packets and if a collision occurs on the way then what to do further.
Before sending the packets on the shared network segment the sender checks the shared network medium whether it is free or not. If it is free then the sender starts to send packets on the shared medium and it also checks while sending frames that no other device may send packets on the medium. If anyhow, another device sends the packet on the medium then it may lead to a collision, and in that case, sender devices send a stop/jamming signal and let know other devices that the collision occurs on the shared medium. However, after a certain amount of time senders again checks the shared medium and start to send packets.
Hubs do not support the concept of VLAN and STP. Following are the two types of Huba available:
- Active Hub: These hubs are the connection point for multiple machines and also regenerates, monitors, and amplifies the signal.
- Passive Hub: These are the normal hubs that only acts as a point for multiple connections.
The switch is a data link layer device and it runs on the full-duplex mode that means we may send and receive packets at the same time. It is known as the Intelligent device. It does understand mac address and seeing mac address makes the further decision. It has more ports than the hub. Mostly comes with 24 or 48 ports. You may have the option to change the mode to half-duplex in the switch.
The switch supports the concept of VLAN to segregate the broadcast domain and helpful in network security and the STP(Spanning tree protocol) is used on the switches to avoid layer 2 switching loops.
Difference Between Router and Switch
Switch
- It has multiple collision domains and a single broadcast domain.
- It is used for communication among the devices within the local area network.
- It works on the second layer of OSI model.
- It uses a mac address for the forwarding decisions and maintains mac address or CAM table.
- It uses Full duplex mode for the transmission and you may have the choice to select half-duplex.
- As it operates on full-duplex and thus there are no chances of a collision.
- We cannot use NAT with switches.
- We can use the concept of VLAN to segregate the broadcast domain in the switch.
- It uses STP(Spanning tree protocol) to avoid switching loops.
We may also perform routing on switched but for that, we need to use Layer 3 switch
Router
- It has multiple collision and multiple broadcast domains.
- It is used for communication among the different LANs or network.
- It works on the third layer of the OSI model.
- It uses the IP address for the forwarding decisions and maintains the routing table to choose the best route.
- It also uses Full duplex mode for the transmission.
- It also operates on full-duplex but it may have collisions sometimes.
- We can use NAT(Network Address translation) with Routers.
- Routers do not understand the concept of VLANs.
- We use routing protocols here and every routing protocol has its own methods to avoid layer 3 loops like RIP uses Split horizon, Route Poisoning, Hold down timer.
- Used for the routing that means show the IP data the best route possible.
Layer 3 Switches
A layer 3 switch works on the third layer of the OSI model. The multiplayer switches can do switching as well as routing also. It is widely used for inter-VLAN routing as we can communicate with different VLANs. We can also use these switches for the routing purpose by using the IP routing command. By default, we cannot give IP to the port of the multilayer switch. For that, we need to type the command ‘no switch port’ inside the particular interface, and afterward, we may set the IP address to the interface.
Switch(config)#ip routing
Switch(config)#int f0/1
Switch(config-if)#no switchport
Switch(config-if)#ip add 192.168.10.1 255.255.255.0
Switch(config-if)#
Above mentioned are the commands to enable the routing in the layer 3 switch and by using no switchport command the interface of layer 3 switch acts as a router interface.
Different Types of Switch In Networking with their capabilities
There are different types of switches available in the market that you can use according to the requirements:
- LAN Switch: These switches are used within the LAN environment of the company. It is a single point of connection for multiple computers within the company. These switches help to reduce the network congestion or bottlenecks by assigning data packets to its final recipient.
- Unmanaged Switches: These switches are widely used in the house and small business environments as there is no need for any configuration. You just need to connect the device to switch and afterward there is no need for configuration. It is used to connect computer to computer, computer to a printer. These switches can be set up very easily without wasting any time and they are economical also available at low prices than the managed switches.
- Managed Switches: These switches are used by big corporates and the ISPs as these switches provide several features like Quality of Service, SNMP, Switching and routing, and many more. To configure these switches we need network admin and IT professionals as they need to be configured correctly.
- POE Switches: These are Power Over Ethernet switches that use PoE technology. Every port of the switch provides some power so that other networking devices can be attached to switches to use it. These switches are capable of doing both the data transmission and providing power over the Ethernet cable at the same time. Four wires used for the data transmission and four wires used for the power over Ethernet. There is by default power that gets transferred to devices when we connect devices to switch port and we are allowed to change it by using some commands.
- Stackable switch: It is also a network switch that can operate standalone and with a group of switches as well. Generally, in the production environment, we use stacking technology to do the stacking of multiple switches. In the stacking process, the group of switches is stacked together like we have made a group of 8 switches and we create a single switch master here then by using the master switch we may manage the other switches also. Now, all the switches behave like only one switch. We don’t need to configure every switch separately.
Modular Vs Non-modular Switch
Modular switches are also used in the network and provide us the capability to change the parts of these switches. These switches can be modified according to the increasing needs of the business and users. The components which are usually changes or replace:
- Network interfaces using line cards
- Cooling fans
- In case of failure, power supplies can be changed.
Non-modular switches are also used in the network but with the fixed configuration i.e. with the limited number of ports and they are not expandable and thus cost of these switches is also low. These include unmanaged and smart switches
Stackable vs Non-stackable Switch
Stackable switches are network switches that can operate standalone and with a group of switches as well. Generally, in the production environment, we use stacking technology to do the stacking of multiple switches. In the stacking process, the group of switches is stacked together like we have made a group of 16 switches and a single switch master needs to be created and then by using the master switch, we may manage the other switches also. Now, all the switches behave like only one switch. We don’t need to configure every switch separately.
Non-stackable switches are the standalone switches and they don’t have stacking port in the back for the configuration of stacking technology that means these switches cannot be combined to form a single virtual switch and thus we need to configure every switch manually.
Difference between Managed and Unmanaged Switches
Managed Switches give functionality to network admins to manage and have control over the LAN traffic and it provides security by using SNMP, Access-lists, NAT. By using these switches Quality of Service can be achieved.
Unmanaged Switches are widely used in the home and small business environments as there is no need for any configuration. You just need to plug and play the devices. It is used to connect computer to computer, computer to a printer. These switches can be set up very easily without wasting any time and they are economical also available at low prices than the managed switches.
How to Configure Network Switch Step by Step
In the Network switch we have three modes, first is user exec mode, second is privilege mode and third is global configuration mode. All the configuration part is done on the global configuration mode.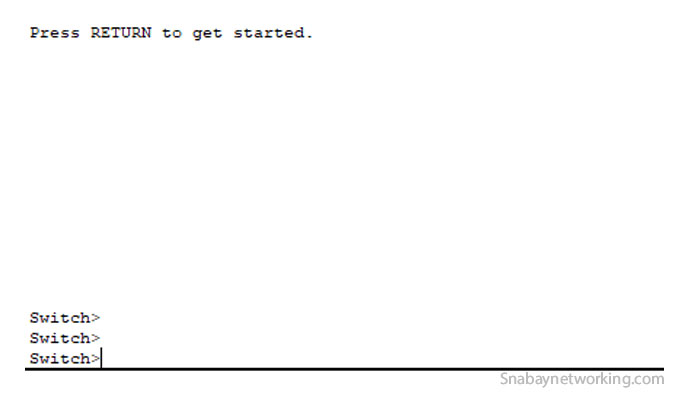 The above screenshot is the user exec mode.
The above screenshot is the user exec mode. To move to privilege mode, you need to type enable in the CLI of a switch. Refer above screenshot. To move to global configuration mode, you need to type the configure terminal in the CLI of a switch. Refer above screenshot.
To move to privilege mode, you need to type enable in the CLI of a switch. Refer above screenshot. To move to global configuration mode, you need to type the configure terminal in the CLI of a switch. Refer above screenshot.
To change the hostname of the switch, we use hostname command with the hostname like in our case we set hostname to Host1, and to go inside the interface we use the command interface with the interface name. Refer above screenshot.
To check the configuration of the switch we use show running-config command and this is the running configuration that is available on the RAM of a switch.
If you want to configure the console port then use the above-mentioned commands in the screenshot. Here, we are entering the console by using line con 0, and then we set a password as Cisco123 and we enter the login command to enable password checking and now whenever you try to enter to switch, you will be asked to enter console password.
To configure telnet, see the above-mentioned commands in the screenshot. By using command line vty 0 4, we are configuring telnet for 5 users i.e. five users may access this switch at once then we set a password as cisco and enter login. We need to enter enable password ccnp123 command also, here ccnp123 is the password. While accessing the switch, we need to enter the password as ccnp123 to move to privilege mode from user exec mode.
Advantages and Disadvantages of a Network switch
Advantages
- Helpful to increase the bandwidth of the network.
- Helpful to reduce the workload on the specific host.
- Increases network performance.
- Fewer frames collision due to the separate collision domain for each port of the Network switch.
- Loop avoidance mechanism using STP(Spanning tree protocol).
Disadvantages
- Broadcast traffic may create issues.
- If you stuck in network connectivity issues then troubleshooting would be difficult.
- You need to pay some more money to buy these switches as compare to hubs and switches.
- They need to be deployed in the proper way to handle the multicast packets.
- Limiting the broadcast would be complicated.
List of Cisco Switch Series and its specifications
| Switch Series | Specifications | ||||
| Cisco catalyst 9500 Series | Layer 2 and Layer 3 switches stackable core | ||||
| Cisco catalyst 9300 Series | Stackable access and distribution switches for layer 2 and layer 3. | ||||
| Cisco catalyst 9200 Series | Stackable access switches for layer 2 and layer 3. | ||||
| Cisco catalyst 3850 Series | Stackable access and distribution switches for layer 2 and layer 3. | ||||
| Cisco catalyst 3650 Series | Optional stacking capability switches for layer 3 and layer3 | ||||
| Cisco catalyst 2960 -X/XR Series | Stackable access switches for layer 2 and layer 3. | ||||
| Cisco catalyst 2960 -L Series | Access switches for layer 2 and layer 3. | ||||
| Cisco catalyst 3560CX/2960CX Series | Compact, fanless switches for layer 2 and layer 3 | ||||
| Cisco Catalyst Digital building series | Compact, fanless switches for layer 2 and layer 3 | ||||


