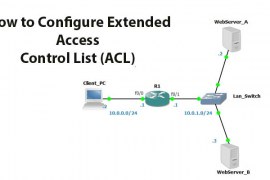
In this section, briefly explains the creation and configuration of an extended access control lists. Before discussing the topic lets defines extended access control lists. The extended access control list is used to control network traffic. The port number, protocol, ...
Snabay Networking Latest Articles
Man in the Middle Attack (Cyber Attack)

A Man In The Middle Attack refers to a kind of cyber attack whose particular motive is to get involved in the conversation someone is having with someone in order to get the sensitive and personal information from both the ...
What is Ping Spoofing

Ping spoofing is the concept of sending fake information into the server. In the Viewer’s appearance, It looks like issues and fluctuations. In this spoofing, the false data acts as the original data packet and sends the data to the ...
Diffraction Has What Affect On A Wireless Signal’s Propagation?

Diffraction Has What Affect On A Wireless Signal’s Propagation? is it bothering you? well. Let’s discuss. A wireless signal can transmit directly from a straight line from the sender side to the receiver side. And this type of propagation uses ...
How to Defense Against Network Attack

Defense Against Network Attack when hackers attack your network, they target every part of it which may help them in either stealing your identity, your finances and your personal details which you surely don’t want anyone to get their hands ...
Limitations of a Wireless Network Connection

Although the wireless networks have made our lives mobile, faster, accessible, convenient and well connected, they have their own limitations. These limitations are inherent in their designs, ranges or other vulnerabilities that they might suffer. To know more about the ...
Data Transmission- Serial transmission, Parallel Transmission
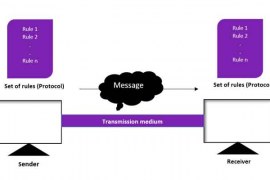
Let us know about data transmission: It is the process of sending the data between digital devices. In analog or digital format the data is sent from one node to another node. Devices will communicate with each other by sending ...
What is Local Area Network (LAN), Advantages and Disadvantages
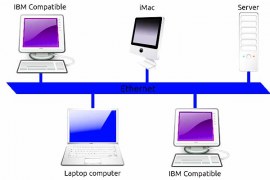
When a Network connected to a limited number of computers or systems within a small geographical area is called the local area network. We have different topologies to administrate the structure of the local area network. Let us discuss each ...
Leading Intrusion Detection System (IDS) Products

As the technology advances towards it is prime, we are facing the challenge of securing it from being used wrong. The biggest concern today is preventing hackers from accessing the network and devices they no rights to. But it’s easier ...
Introduction to Network Protocol Analyzer (Sniffers)

Known by many other names such as Network Analyzer, Protocol Analyzer, and Packet Analyzer, Network Protocol Analyzer is an important sniffing tool in the network administration. Without it your network management is incomplete. It comes in the form of both ...