Perhaps the most sophisticated form of communication in today’s world is the e-mail which also seems to a legitimate successor to the letters. Based on the same format and writing style, email is not more than an electronic form. For ...
Snabay Networking Latest Articles
What is Wired Equivalent Privacy (WEP)

As a part of IEEE 802.11, Wired Equivalent Privacy (WEP) has been specified as one of the security protocols and a part of the algorithm to provide the customers with as much data confidentiality as the wired technology, devices, and ...
Institute of Electrical and Electronics Engineers (IEEE) 802.11 Wireless Standard
IEEE 802.11 Wireless Standard: The Institute of Electrical and Electronics Engineers or the IEEE is a New York-based international professional association of electrical engineers and electronic engineering formed in 1963. IEEE 802.11 is a part of a LAN Protocol standard ...
What is Symmetric Encryption Algorithms

Encryption is as essential for your data as a key is essential for a lock that protects your house. Symmetric Encryption uses the Symmetric Key to encrypt and decrypt information and Algorithms are a part of this whole process that ...
What is Asymmetric Encryption, Cyphertext

When we talk about encrypted communication, we have to keep in mind two parties primarily; the sender and the receiver. The former encrypts and the latter decrypts. Described as the foundation of Public Key Infrastructure (PKI), Asymmetric Encryption key provides ...
What is a Honeypots in Network Security

If you look up the history of cyber crimes(honeypots), there you can find a lot of creative and unique ways that attackers use to victimize their targets. With the possibility of different types of attacks targeting different functions and trying ...
Enterprise Non Public Network (Private Network)
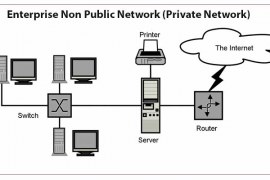
Enterprise Non-Public Network (Private Network): In this age of the internet, all users connected to the internet can send and receive data publicly. But in its primitive form, computer networks were formed by organizations such as universities, military, and research ...
Campus Area Network (CAN) With Example

Campus Area Network was shortly called the CAN. Office, school, any area that presented at a limited distance is called the campus. The Providing of the network at a particular location is called a Campus Area Network. Now How the ...
History of Local Area Network (LAN)
As the world started to get more technologically advanced after the two devastating world wars which changed the power dynamics of the entire world, use of computers in United States of America, one of the few involved parties in the ...
Application Layer Protocols PDF
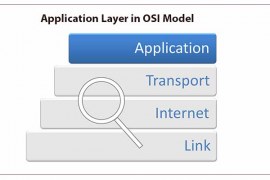
Application Layer Protocols PDF This is an overview of the Application Layer Protocols PDF, if you want to read full article in best quality in pdf, we have provided download link below. The seventh and the topmost layer in the ...

