We have many types of devices. It may be networking devices or it can be intermediary devices that present in the computer network. Let us learn about various types of devices that are present in the computer network. There are ...
Snabay Networking Latest Articles
Basic Switch Configuration

To know about basic switch configuration, let us first use a packet tracer network simulator software. Any network simulator can be used or also a real cisco switch. Until the selected software which you are using is containing the commands, ...
Attacking Network Protocols PDF Download

Were you searching to download Attacking Network Protocols PDF? Well, you are at right place. I have given the download link of the pdf below but before that please go through the table of content of the pdf to know ...
What is Network Security

Specialized networks that are built to protect your network’s usability are known as network security. The protection provided by the network security system is extended to your data too. Usually, your network security system protects the integrity of your network ...
What is Administrative Distance, Metrics

An administrative distance when two or more routing protocol configure in the network for transmitting data source to destination. An administrative destination defines which route or routing protocol will be best to transmit data. Lower the value higher the priority. ...
SYN Flood Attack in Network Security

SYN Flood Attack: Short for Synchronize Flood Attack, an SYN is a type of DoS attack. Basically, the SYN is used to establish communication between two devices over the Transmission Control Protocol and Internet Protocol (TCP/IP). As the name itself ...
What is POLAN (Passive Optical Local Area Network)
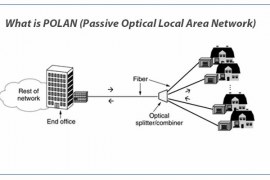
In the earlier times for telecommunication or for enabling an internet connection copper wires were used. Optical Fibre, later on, replaced the copper cables due to advantages such as greater bandwidth, faster speeds, reliability, the capability to carry information over ...
How to Access Another Computer Through IP Address
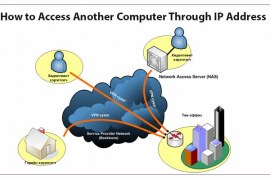
To understand the term remote access, let’s put it down in simple away. Access by remote (location). Imagine you’re planning to take a long holiday to relax and rejuvenate by spending some time alone or with family on a nice ...
Mesh Topology Advantages and Disadvantages

A Mesh Topology is a connection of multiple hosts to a single host. It is connected in the point to point representation, a single host connected to all hosts in the network. The Mesh topology hosts work as a relay ...
Star Topology Advantages and Disadvantages
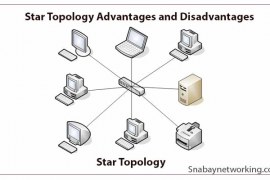
A Star Topology is basically a network structure where multiple devices (nodes) are connected to one central unit individually, making the shape of a star if you look at its’ structure. In this network structure, signal and data are transmitted ...

