Can you imagine leaving your house unlocked when you go out and not getting robbed because of your stupid mistake? Chances are you are not likely to escape a theft on your property if you do such a thing and ...
Snabay Networking Latest Articles
How to Minimize Direct Denial of Service (DoS) Attack Impact

Denial of Service Attack and Distributed Denial of Service Attack (abbreviated form; DoS for former and DDoS for latter) are almost the same things. Sometimes a DDoS attack is put into the records as a subcategory of a DoS attack ...
SQL Injection Attacks in Cyber Security

SQL Injection Attacks in Cyber Security: SQL Injection Attacks in Cyber Security: Structured Query Language (SQL) is the domain language which is used in handling structured data and managing database for building customized. When targeted in a cyberattack, it is ...
What is Loopback Interface in a Cisco Router
The loopback interface is the virtual interface that is always available and ready to be used, it is not mandatory that it will be tied with 127.0.0.1 it an interface like any other interface that could have its own IP ...
What is a Subinterface in a Cisco Router
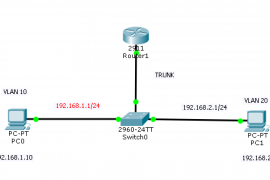
A Subinterface is a virtual interface that is created by dividing one physical interface into many logical interfaces, the subinterface uses the parent physical interface in order to send and receive messages like Fast Ethernet 0/0.1 is the subinterface Fast ...
Advantages and Disadvantages of Network Address Translation (NAT)
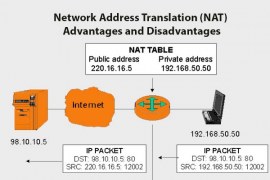
As the name suggests Network Address Translation (NAT) is nothing but it is a process of converting local IP addresses into the global IP addresses and global IP addresses into the local IP addresses. In the 1990s the number of ...
What is Internet and its Uses?
Internet, firstly we can talk about what is Internet? well, It is a Global Network mostly used in computers, mobile phones, tabs, and laptops, etc to get information, news and for the purpose of communication. To know more about What ...
Basic Networking Concepts PDF Download

Are you searching for Basic Networking Concepts PDF? Well, you are at right place. I have given the download link of the pdf below but before that please go through the table of content of the pdf to know what ...
Sniffer Attack in Cyber Security

Sniffer Attack in Cyber Security: A sniffer software is one of the non Malicious Software that is put to malicious use. Not only software, but it also comes in the form of a hardware device. Inherently, it is used for ...
What Type Of Delivery Uses Data Link Layer Addresses?

Want to know what type of delivery uses data link layer addresses? alright, let’s discuss. ARP(Address resolution protocol) is used to deliver the data link layer addresses. The ARP is a protocol used to resolve the IP addresses to the ...