Computer Peripherals PDF This is an overview of Computer Peripherals PDF, if you want to read full article in best quality in pdf, we have provided download link below. The computer peripherals are devices. We connect the peripheral devices externally ...
Snabay Networking Latest Articles
What Are Two Types Of Ipv6 Unicast Addresses?

In this article we are going to discuss the Two Types Of Ipv6 Unicast Addresses so let’s go for it. Normally, in the IPV6 unicast address classification, there are three types. Unicast, Multicast, and anycast. Like the IPV4 classes, the ...
Network Interface Card – Types, Working, Advantages and Disadvantages

NIC represents as network interface card or a network interface controller or LAN card. Why do we even use a card in a network? What’s the use of this hardware component to even use in the network. Doesn’t we only ...
What is Computer Network with Examples

To know the definition of the Computer Network. Let us discuss the simple definition of the Computer Network. A computer network is a set of communication elements that are connected by communication links. The definition tells the set of elements ...
What Is A Role Of The Logical Link Control Sublayer?

What is the role of the logical link control sublayer? Let us discuss the role of the logical link control sublayer. The IEEE 802.3 standard will describe the functions of the Logical link sublayer. In the OSI model, we have ...
What Is The Function Of The Kernel Of An Operating System?

What is the function of the kernel of an operating system? Everyone may have heard the word computer. Now we will discuss the basic introduction about the operating system, and what does a kernel does in the operating system. It ...
What Is A Characteristic Of A Converged Network?

Characteristic Of A Converged Network The Network system always got changing and changing in our evolution Technology. There are many different types of data traffic that can be found in our modern networks. Audio, video data and the multiple services ...
Access Control Lists (ACL) | Standard, Extended and Named ACL
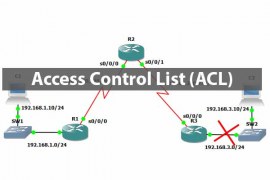
Access Control Lists are used to filter the packets to avoid traffic in the network. The security is provided to limit the traffic. By using the name or number ACL is identified. Filtering is used in the access list and ...
What Hard Drive Technology Is Used To Predict When A Drive Is Likely To Fail?

You might be wondering about What Hard Drive Technology Is Used To Predict When A Drive Is Likely To Fail, well. To know how devices get failed and when they are going to fail. We have to check some of ...
Extended ACL Established Keywords | Cisco ACL Established Example
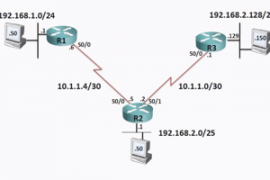
This article provides a brief description of the Extended ACL Established Keywords. Before discussing the topic let’s summarize the overall topic connected to the topic. Access control lists are a group of conditions that are wrapped together by a particular ...

