What is Hacking
Hacking refers to the act of compromising the Security of Target System and gaining unauthorized access to it. It targets Confidentiality, Integrity, and Availability of the System. Various tools and techniques such as Malware, Worm, Trojan, backdoors, DoS Attacks, phishing, Scripting, Shellcodes, password cracking, wifi cracking, are used in Hacking Activity. The objective of performing such activities could be either curiosity, thrill, power, revenge, financial gain, etc.
Who are Hackers
Hackers are not the bad guys always. Some Hackers work to strengthen the target System whereas some to collapse it. In this article, we would be discussing various types of hackers and the way they are categorized. In most basic form, Hackers are the individuals having the ability to exploit the vulnerabilities in the target system.
Hackers are the individuals who possess excellent skills in Computer Hardware and Software domains. They have the ability to asses the target system, identify weaknesses in it by carefully inspecting the system, exploit the weaknesses in the target system, and cover their tracks.
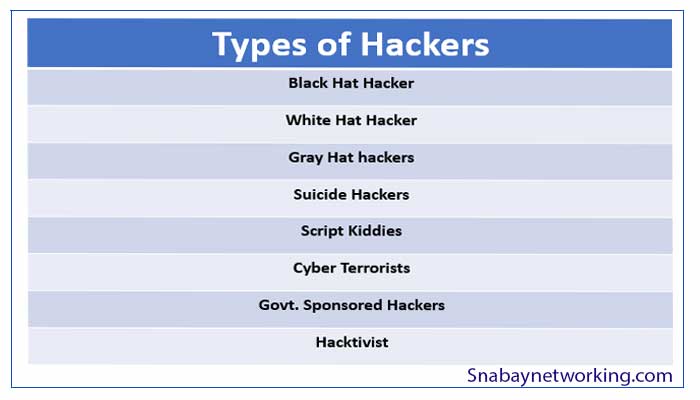
Types Of Hackers
Depending on the intention, nature, and capabilities of Hackers, they are classified in the below Categories.
- Black Hat Hacker
Black Hat Hackers are individuals who penetrate the system without authorization from the owner. They do not leave traces of the attacks. Black Hat Hackers use their hacking skills for malicious activities. They possess extraordinary skills in the Computer hardware and software domain.
- White Hat Hacker
White Hat Hackers are the individuals who penetrate the System with proper approval from the Owner of the System. Their objective is to identify the weaknesses in the system so that they could be fixed before the real bad guys identify them. White Hat Hackers act defensively to secure the IT infrastructure against malicious attacks. White Hat Hackers are also called Penetration Testers.
Most Big Organisations hire White Hat Hackers to identify the weaknesses in their System. The act performed by White Hat Hackers in such a case is termed as Vulnerability Assessment and Penetration Testing.
- Gray Hat hackers
Gray Hat Hackers act both defensively and offensively at various times.
- Suicide Hackers
Suicide Hackers aim at collapsing the critical target System or Infrastructure for some reason and do not worry about any kind of punishment. They perform hacking activities without caring about their act getting identified. They are ready to sacrifice their life just like suicide bombers.
- Script Kiddies
Script kiddies are individuals who do not possess proper hacking skills. They usually try to attack and compromise systems using some readymade tools, scripts, and techniques to accomplish their tasks.
- Cyber Terrorists
The Objective of Cyber Terrorists is to create environment fear and grief by performing large-scale attacks. They are usually directly linked with real Terrorists/ Criminals.
- Govt. Sponsored Hackers
These types of hackers are employed by some government departments to perform attacks against their target Infrastructure.
- Hacktivist
The individuals promoting their social or political motives by utilizing hacking skills are termed as Hacktivists. They usually compromise the Government or other related agencies as an act of their protest.
Also, Read…
Download What is Hacking, Types of Hackers and How Hackers are Classified in pdf – Click here