What is the aim of an ARP Spoofing?
To understand the aim of ARP spoofing attack, let us first discuss What is an ARP ? and the definition of Spoofing.
Definition of Spoofing
Spoofing is an attack, developed by Third-party users into the systems or IP networks to capture or falsify the Original data. That means a person or a system erases the original data by modifying it with the falsified data.
The IP protocols, TCP/IP suite protocols don’t use any mechanisms to authenticate the authorized person. If one application doesn’t take specified precautions to identify the Authorized user, many spoofing attacks may occur in the Network.
They are different types of Spoofing attacks. They are
- IP spoofing
- ARP spoofing
ARP Spoofing
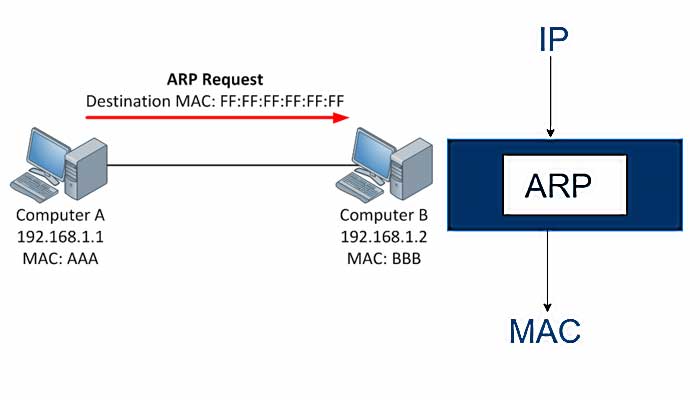
The term ARP stands for Address Resolution protocol. In this, The Unauthorized user or a falsified user will send a message to the local area network by using the fake Address Resolution Protocol (ARP).
In the Address Resolution Protocol, we have two types of attacks. They are the Logical address and the physical address. The Logical address means the IP address and the Physical address means the Mac address of the Network.
How the ARP spoofing gets attacked?
In the Network, most of the data can communicate through the logical address, but at the back of the network, we use the physical address over the network. For Example, one person wants to send a message to the other person, the sender should know the mac address that means the physical address of the network called the address resolution protocol.
Let us consider an example to understand the working of the ARP protocol. In the Address resolution protocol, when User A wants to send a message to User B, then User A sends a packet to all the devices in the network. The packet consists of the IP address of User B. Now when the packet reaches the network, the devices with the same IP address will reply to User A. The message will be delivered to all devices in the network, but only User B reply to the message since User B’s address matches the IP address sent by User A.
This concept we call the address resolution protocol.
Now, how the ARP spoofing occurs while transmitting the data over the network?
It is an attack in which the malicious user sends the false ARP address over the local area network. In the local network, every computer has the access to the router or is directly connected through a switch. Every computer user within the network updates its IP address. The entire lists of all IP address are present in the router or a switch.
We can find all the IP address present in the network with an ac command called ” arp -a”.
Here the Third-party user fills the network with all falsified IP addresses. At the time when User A wants to send a packet to User B, the third party user sends the packet with the same IP address and different MAC address. When all the computers receive the packet from the third-party user, they immediately save the new MAC address in the network, and User B sends a message to the Third-party user instead of User A. Now, all the messages can be accessed by the third-party user (Unauthorized user).
I hope you now you have cleared what the Aim of an ARP Spoofing Attack is.
Also Read: