Rules used to reduce network traffic and network attack. ACLs are used to filter the incoming and outgoing network. The ACL contains two types of list and the Extended Control List is one among them. The extended access control list contains different traffics such as ICMP, TCP, and UDP, etc. To know more about the Extended Access Control List (ACL), keep reading this article till the end.
In an extended control list, they can differentiate the IP traffic, unlike the Standard Access Control List. In Extended ACL they use both source and destination address and the port number to differentiate the IP traffic. Here we can define which IP address needs to be allowed or get denied and the range is from 100-199 and 2000-2699. Extended control list filter packets which are near to source address. Otherwise, if the extended access control lists are placed in the destination network they will use the bandwidth till the packets reach the destination and the unwanted traffic will get filtered till the final destination.
Extended Access Control list is the firewall protection that needs to be created to protect the filtering packet from the network. Here, for example, a figure is shown below which explains in detail. A router is connected to the internal interface and external interface. The internal interface has 192.168.8.0/24 segment having address 192.168.8.1/24 and the external interface has a 10.0.2.0/24 segment having address 10.0.2.1/24. Here we need to manage the 192.168.8.0/24 network and the rest of them are managed by certain groups. In the network 192.168.8.0/24, the permission granted to users to access only the web servers which are outside the network. For this purpose two ACLs needed to be created 101 and 102. Access list 101 is used to control the traffic leaving the office and access-list 102 to control the traffic from unknown networks.
We can create and configure the extended access control lists using an access list and access-group command respectively.
FEATURES
- To the source, they seem to be closed but not.
- Based on the source address, a destination address, and the port number the packet filtering takes place.
- Specified services will be accessed or denied in extended ACLs.
- A range created for ACL is from 100-199 and can be extended to 2000-2699.
- Extended control list rules can’t be deleted if it happens all the access lists will be deleted.
- Extended ACL with named can have the flexibility to delete the rules.
CONFIGURATION
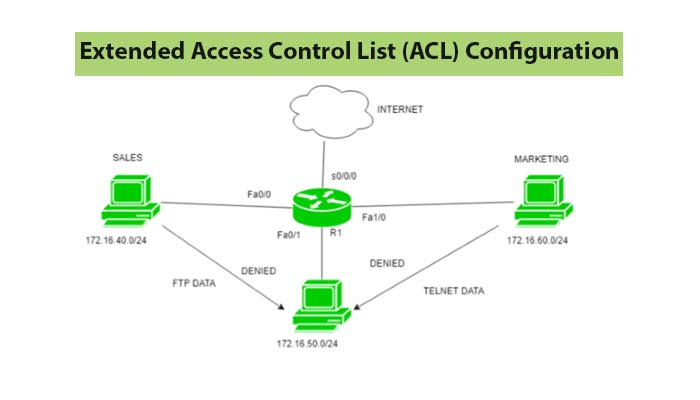
The figure shown above contains 3 departments finance, sales, and marketing. The network used by different departments such as sales is 172.16.40.0/24, the network of finance is 172.16.50.0/24, and marketing is172.16.60.0/24. The next step used is to delete the FTP connection from sales to finance and telnet connection from the finance department needed to delete from the marketing and sales department.
Also, read…
- Access Control Lists (ACL) | Standard, Extended and Named ACL
- Extended Access Control List (ACL) Operators
- How to Configure Standard Access Control Lists (ACL)
Download Extended Access Control List (ACL) in pdf – Click here