Domain Name Server (DNS) is nothing but a phonebook of the internet. DNS is a protocol that is used commonly on the internet, and so you may hear a lot about the DNS attacks on the internet. We access the information on the internet through the domain names, for example, “nytime.com” or “espn.com, etc”. Web browsers can interact through Internet Protocol (IP) address. The main role of the Domain Name Server is to translate the domain name to the IP address so that the internet resources can be loaded by the browsers.
There will be a unique IP address for every device that connected to the internet. This address is used by other machines to find the device that it wants to communicate. The Domain Name server eliminates their needs for humans by, memorizing the IP address like 192.168.1.1 (in IPv4), a very complex alphanumeric IP address in IPv6.
How does the DNS work?
The main work of Domain Name Server (DNS) is to convert the hostname (like http://www.example.com) into an IP address like 192.168.1.1 which is computer friendly. Each device on the internet should have an IP address and this address is used to find the appropriate internet devices like we use the street address to find a particular home.
Whenever a user tries to upload a webpage, a translation must be needed between what a user type to the web browser and also the computer-friendly address for finding the necessary web page.
For understanding the process of the DNS resolution, it is very important to study the many different hardware components through which the DNS query must pass through. For the web browsers, the DNS lookup happens “behind the scenes” and no need of any interaction from the computer of the user apart from the request made initially
How DNS adds efficiency
Domain Name Server helps the things to run quickly and smoothly. Now let’s imagine that you want to visit networkworld.com.
First, the request for getting the IP address is given to the recursive resolver (Server that works by an ISP or by third-party provider). The recursive resolve will know to which all DNS servers it needs to ask for resolving the name of the site by its IP address.
This search is also handover to the root server (who knows all the information about the top-level domain like .com, .org, etc and also the country domains such as .cn (China), .uk (United Kingdom)). The root servers are present all around the world so that the system will allow you to the nearest one geographically.
When the request reaches the root server, it will go to the top-level domain name server that stores the data for the second-level domain (for example the data for networkworld.com is network world). After that, the request will go to the Domain Name Server that contains the data about the site and the IP address. When it gets the IP address, it is given to the client, so that the client can use it to visit the website.
DNS Reflection attack
To knock down the internet pipe the DNS reflection attack is used in any type of denial of service (DDoS) attack. This attack can be classified into two-step of attack; here the attacker will send a huge amount of request to one or more than one DNS servers when the spoofed source IP of the target victim is used.
The DNS server that gets the semi-legitimate request will reply to the spoofed IP, so unknowingly starting an attack on the victim that is targeted by sending the response to the request that was never sent by the victim.
The Domain Name servers are offered as open resolvers on the internet that will serve any request that sent by them, some report says the amount in millions. This large number makes it difficult to pre-identify the attacker using IP reputation. Moreover, the servers can be defined as legitimate servers that mainly send legitimate traffic that makes confusion in IP reputation service about whether or not their nature is malicious.
Most of the DNS queries are sent by using UDP; here the protocol won’t allow source IP validation. So that the Domain Name server assumes that the request is arriving from the victim and the replies are sent back to them.
Due to IP spoofing it became difficult to detect the attacker the victim because it appears as if it is attacked by a legitimate DNS server and the attacker has the hidden IP address. IP reputation service is invaded by the IP spoofing because it assigns a bad reputation to the legitimate DNS server. It also changes the tractability so that the security experts can identify the source of the attacker.
One of the advantages of spoofing is that the attacker can attack the server or service. The victim’s public server IP and the port can be used by the attacker for making sure that not only just DNS service but any server can be attacked. The traffic in the network simply looks like a lot of data and the server have to parse and check the data to confirm that it is not legitimate traffic.
Note that in this attack IP spoofing also have limitations – If IP spoofing is not possible, then the attack cannot be done because there is no other way to inform the responses to the victim’s IP. This is how the bot called Mirai running on IoT devices with the help of a router that performs NAT. Recently Mirai infection is mainly aiming at the home routers itself, by bypassing the NAT limitation.
The biggest and the latest advantage to the DNS flood is amplification by using DNS extensions and DNSSec. EDNS0 will allow the DNS to make a large response than the original 512 which is allowed. At this time the DNSSec allows the authentication of the responsibility for preventing cache poisoning.
The DNSSec needs EDNS0 for operating so that it adds cryptographic data for making the response. Since the DNSSec is getting more popular, it makes the DNS server support the EDNS0 allow the attacker to get a large response to their request.
The size that is possible for the response is only up to 4096 bytes and the attacker is only allowed to send a small number of short requests and the replies sent by the DNS servers are amplified highly by exhausting the victim’s internet piping.
The attacker can learn about the DNS server and find about which legitimate queries can give a large number of replies and it also uses the DNSSec for making them bigger with the cryptographic data. In many cases, the size of the response gets to its maximum of about 4096 bytes that creates an amplification factor x100 for the entire original request.
In the present, the internet connectivity is very large. When a 100 M connection is a connection to the internet, it will send a modest attack on its own and so it will cause some damage to the normal sight.
However, if an attacker can use his large 4096 bytes response for the attacker’s 44 bytes request and will get a 100x amplification, and so the server of the attacker will get a 10G of attack traffic, which is above its normal bandwidth. This kind of traffic will make any normal service to immediately change out of service. Just imagine that what can be gained by a botnet or even a few of such bots.
Other than the size of the response there is also another fact that is the response that cannot fit into a normal IP packet. In this kind of case, the servers will use the option of IP fabrication, which allows them to split the message into several packets.
The attack will become harder by using fragmented traffic in the attack – here the mitigator wants to store their first packet’s layer data to the table and this wants to be applied to the remaining packets from the dame message. Many network entities are exhausted very fast with much-fabricated traffic that makes this attack very efficient.
After learning about the ins and outs of the Domain Name Server reflection, one thing is left – how to protect an organization from such kind of attack and how to mitigate it? Other than the sophistication of attack itself, there is also a solution for this kind of problem–for mitigating a DNS reflection attack, you need to use a good detector on-site for quickly detecting the attack and prevent downtime.
The detector has to be very smart so that the detector can understand that the attack it sees is saturating the internet connection and so the traffic should be diverted to the cloud scrubbing center. When the traffic is sent to the cloud scrubbing once then it will be cleared and it will be sent to the site.
And this scrubbing depends on the amount of traffic which is similar that is considered legit – will the site see many UDP traffic? DNS traffic? Fragmented traffic? And if so, what differentiates it from a traffic attack? By using an automated technique for separating the legitimate and the attack traffic will provide you better and fast cloud mitigation.
What is Domain Name Server (DNS) Cache poisoning?
Imagine a prank of senior year students in a campus; the seniors in the high school change all the classroom numbers of their high school campus, so that the coming new students who don’t know about the campus layout will go to the wrong classrooms. Now just imagine that the changed classroom numbers will get recorded in the campus directory, and the students will use the wrong classrooms until someone notices and correct it.
Like that DNS cache poisoning is an act that adding false information into a DNS cache, because DNS queries give back an incorrect response and the users are directed to the wrong websites. DNS cache spoofing is also called as DNS spoofing.
The IP address can be considered as ‘room numbers’ of the internet that allows the traffic of the web to teach at the right location. DNS resolver caches can be considered as the ‘campus directory’, and when the store the wrong information, the traffic will go to the wrong places until the cached information is corrected.
There is no other way for DNS resolvers to check their data present in the caches, wrong DNS information will be there in the cache until the time to live (TTL) become expire, or until manually removing it.
There is much vulnerability that makes DNS poisoning possible, but the main problem is that the DNS was made for smaller internet and it was based on the principle of trust (like BGP). One of the very secure DNS protocols is called DNSSEC and it aims to solve some of these kinds of problems, but the problem is that it is not widely adopted yet.
What do DNS resolvers do?
The main function of Domain Name Server resolver is to provide clients that have the IP address which is associated with a domain name. In simple words, we can say that they take website addresses that are humanly readable such as ‘cloudflare.com’ and convert them to IP addresses this is machine-readable. Consider that when a user wants to open a website, his operating system sends a request to the DNS resolver. The DNS resolver will respond with an IP address, and then the web browser will take this address and start loading the website.
How does DNS caching work?
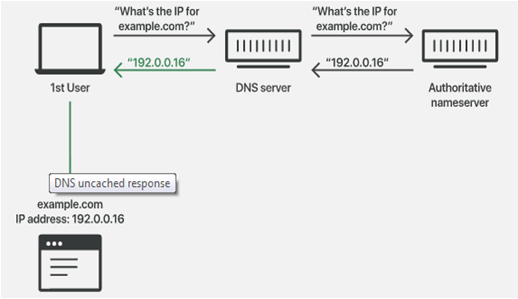
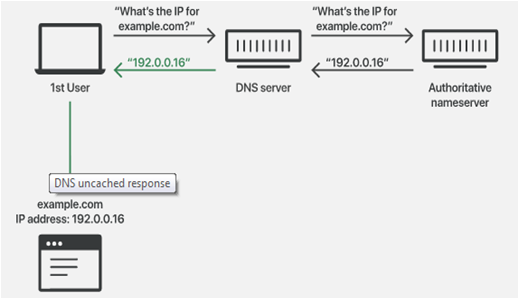
The DNS server will save the responses given to the IP address queries for a particular time. In this way, the resolver will respond to the quires that come in the future very quickly, without the need of communicating with the servers that involve in the particular DNS resolution process. The DNS resolvers will save the responses that given to the IP address in their cache for a long time as the designated TTL that associated with that IP address allow them.
DNS Uncached Response
DNS Cached Response
How do attackers poison DNS cache?
The attackers will poison the Domain Name Server cache by impersonating the DNS nameservers, which means it requests the DNS resolver, and after that, it will forge the reply DNS resolver quires a nameserver. This will only happen when the DNS server uses a UDP instead of TCP, and presently there is no checking of DNS information.
The figure shows the DNS cache poisoning process:

Poisoned DNS cache:

TCP needs both communication parties for performing a handshake to start communication and to check the identity of the device, so used UDP (User Datagram Protocol) is used for requesting and responding. But UDP will not give any guarantee that the connection is open, that the receiver is ready to receive or who is the sender. Because of that, the UDP is vulnerable for forging – here an attacker can send messages by UDP and can act like that it’s a response given by the legitimate server by forging the header data.
When a Domain Name Server resolver accepts the forged response, then it will accept cache the data uncritically because there is no other way to check the information is correct or not comes from a true source. DNS was developed in the early days of the internet, at that time the only parties that connected to the internet was the universities and research centers. And there was no prediction that anyone would spread fake information about DNS.
The DNS poisoning attack is not an easy thing because DNS resolver mainly queries the authoritative nameserver, the attacker will get only a few milliseconds to reply with the fake information before the actual reply from the authoritative nameserver arrives.
The attacker also can access the DNS resolver in some other way. If any malicious party gets the physical access to a DNS resolver, then the attacker can alter the cached data ore easily.
In networking, a port is considered as a virtual point for receiving the data. Computers have multiple ports for making connections with other devices and to have communication with each other, certain ports have to give for certain kinds of communication. For example, HTTP communications are done through port 80 and HTTPS always uses port 443.
DNS Resource Exhaustion
The attackers found that the Domain Name Server is often an unwanted back door that makes invasion into the network of organizations very easily. DNS resource exhaustion is the main threat area where we can see the growth. The DNS has an open nature that makes leveraging it for resource exhaustion and so the attackers highly choose it.
For performing this attack the attacker should have a registered domain and designated the intended target’s name server as an authoritative server or can use an existing domain whose authoritative server is already considered as the intended target.
Then by using a botnet of compromised machines, the attacker gives direction to the machines to send a huge number of requests through any known resolvers so that they will be in an ISP’s network. In each request, it contains a unique, randomized, and also non-existed sub-domain of the domain which is previously registered.
Because of this unique nature of the sub-domains, each request that sends will trigger a recursive lookup which is against the target’s name server. As the attack gets big, the request that getting into the intended target’s name servers also increases. So that the target’s DNS infrastructure will get buckle because of the load by system resolution depletion or network saturation or by both.
What is DNSSec?
As you know that the Domain Name Server is mainly used for translating the domain name to numerical internet addresses (like 198.161.0.1).
As this address system is very helpful for the computers to read and process the data, which is quite difficult for the people to remember. Whenever you need to check the website you need to remember the IP address of the machine to know the location. As a solution to this problem, the numeric IP address will be attached to every domain name. So the website addresses that we use are the domain name. Domain names are stored and accessed on domain a name server which is a special server.
The top portion of the DNS resides is in the root zone, here the IP addresses and domain names are kept in the databases and it is arranged by top-level domain names like .com, .org, etc.
DNS was not secure when it was introduced, but after being used several vulnerabilities were discovered. And so, as a result, a security system was invented and it is in the form of extensions that could be included in the existing DNS protocols.
Domain name security extensions (DNSSec) are nothing but a set of protocols that will add a layer of security to the DNS lookup and exchange processes, which will become very helpful while accessing websites by using the internet.
Advantages of DNSSec
The main aim of DNSSec is to strengthen trust in the internet. It helps in protecting the user from redirection to unwanted websites and unintended addresses. In this way, malicious activities such as pharming, cache poisoning, and man in the middle attacks are prevented.
The DNS server provides the answers, to make sure if the answer is valid or not the DNSSec will authenticate the resolution of the IP addresses with the cryptographic signature. If the DNSSec was enabled properly then you can ensure that the visitors are connected to the original website corresponding to a particular domain name.
Types of DNS (Domain Name Server)
There are three types of DNS query types and they are
Recursive Query
Here the Domain Name Server client will provide a hostname and the DNS Resolver should answer – it will respond with a relevant resource record or with an error message if it couldn’t found. The resolver will begin with a recursive query process, and it starts with the DNS root server until it gets the authoritative name server that contains the IP address and other data needed for the requested hostname.
Iterative Query
Here the DNS client will provide a hostname and the DNS Resolver should give an answer which is best that can be given. If the DNS resolver contains the needed DNS records in its cache, it gives back them. Otherwise, it will refer the DNS client to the root server or it will choose the nearest Authoritative name server to the requested DNS zone.
Non-Recursive Query
It is a query in which the DNS server will know the answer that has to be given. It will immediately give the DNS record that is already stored in the cache or will query the DNS. In these two cases, there is no need for any extra rounds of quires. The respond is given immediately to the clients
There are three types of DNS servers and they are
DNS Resolver
A Domain Name Server resolver is made for receiving the queries that contain a human-readable hostname like http://www.example.com and its responsibility is to track the IP address of that hostname.
DNS Root Server
While considering the journey from the hostname to the IP address, the root server is the first step. It will provide details for the .com TDL name server of the user’s query like http://www.eample.com. As a return that server will give back the details for the domain “.com” DNS zone, which includes “example.com”.
Authoritative DNS Server
The authoritative name server is the final stop in the name server query – it will take the hostname and give back the correct IP address to the DNS resolver
There are 10 types of DNS Record Types and they are
- Address Mapping record (A Record)
- IP Version 6 Address record (AAAA Record)
- Canonical Name record (CNAME Record)
- Mail exchanger record (MX Record)
- Name Server records (NS Record)
- Reserve-lookup Pointer records (PTR Records)
- Text Record (TXT Record)
- Certificate record(CERT record)
- Service Location (SRV Record)
- Start of Authority (SOA Record)
Also read
